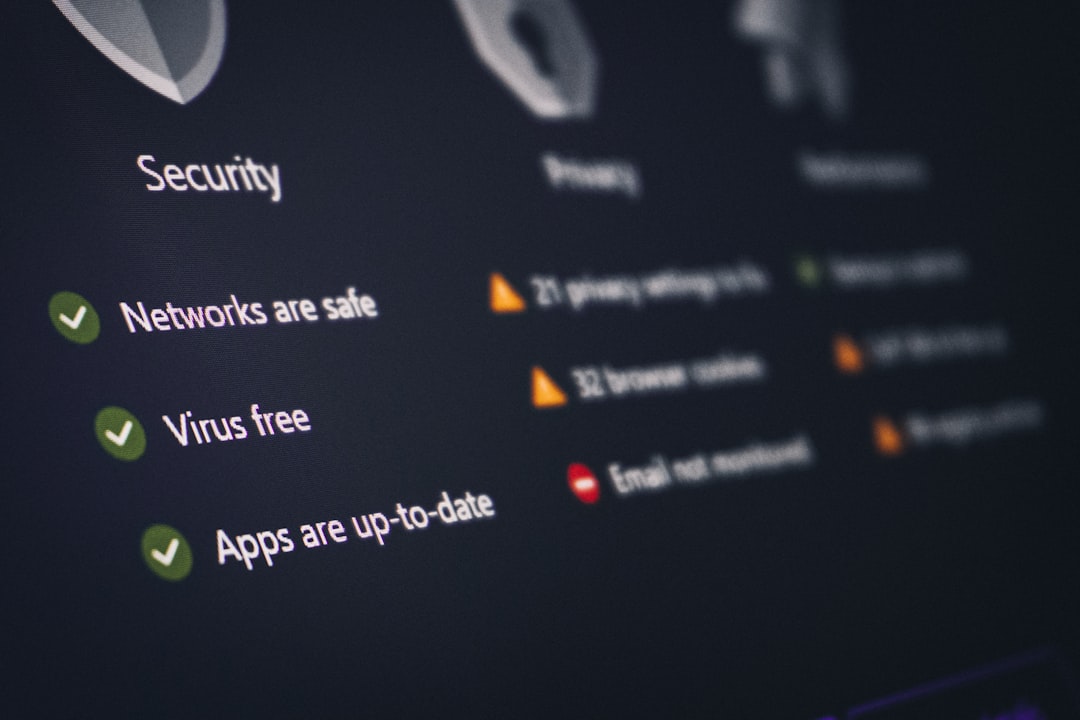
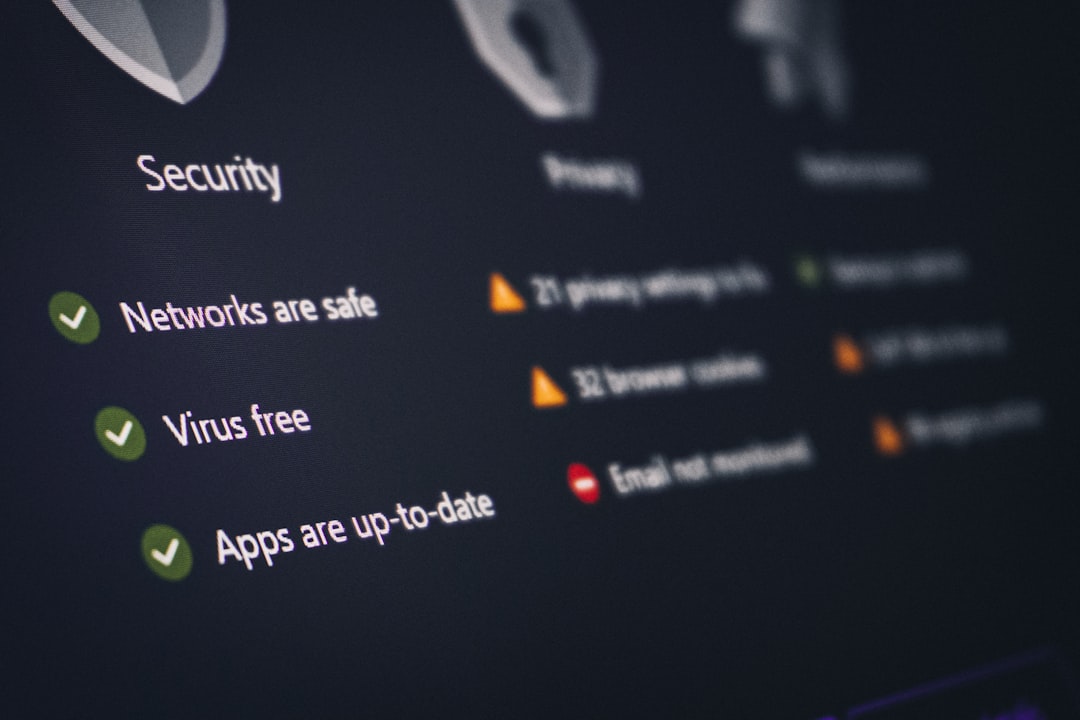
Website security is no longer optional in a landscape filled with automated attacks, data breaches, and increasingly sophisticated cybercriminals. From small blogs to enterprise-level eCommerce platforms, every website is a potential target for vulnerabilities such as SQL injection, cross-site scripting (XSS), misconfigurations, and outdated software exploits. To stay protected, businesses and developers rely on website security scanners—tools designed to detect weaknesses before attackers do. Below are seven powerful website security scanners that help identify vulnerabilities and strengthen overall digital defenses.
TL;DR: Website security scanners automatically detect vulnerabilities such as malware, outdated software, and misconfigurations. Tools like Sucuri, Qualys, Burp Suite, and others provide automated scanning, detailed reports, and remediation guidance. Choosing the right scanner depends on your website size, technical expertise, and budget. Regular scanning combined with proactive patching significantly reduces cybersecurity risks.
1. Sucuri SiteCheck
Sucuri SiteCheck is a popular free online website security scanner designed to detect malware, blacklisting status, injected spam, and defacements. It is particularly useful for website owners who want a quick and accessible external scan without complex configuration.
- Malware detection: Identifies known malicious code on web pages.
- Blacklist monitoring: Checks whether the site appears on major security blacklists.
- CMS vulnerability insights: Flags outdated software versions.
Although it performs remote scans and cannot access server-side files directly, it offers valuable first-line detection. It is well-suited for small business owners and bloggers who want regular checkups without technical setup.
2. Qualys SSL Labs
Qualys SSL Labs focuses specifically on evaluating the SSL/TLS configuration of websites. It provides a deep analysis of encryption protocols, certificate validity, and potential weaknesses in HTTPS implementation.
- SSL certificate verification
- Protocol and cipher strength analysis
- Security grading system (A to F)
This scanner is essential for ensuring secure data transmission between users and servers. A misconfigured SSL certificate can expose sensitive data, reduce search engine rankings, and erode user trust. SSL Labs provides actionable recommendations to strengthen encryption protocols.
3. Detectify
Detectify is an advanced automated security scanner developed with input from ethical hackers. It is designed to simulate real-world attack techniques to uncover a broad range of vulnerabilities.
Key features include:
- Continuous automated scanning
- Detection of over 2,000 known vulnerabilities
- Subdomain monitoring
- Detailed remediation advice
Detectify is particularly valuable for organizations managing multiple domains or complex web infrastructures. Its automation capabilities make it suitable for security teams looking for continuous vulnerability management rather than one-time scans.
4. Acunetix
Acunetix is a commercial web vulnerability scanner known for its accuracy and comprehensive coverage. It identifies issues such as SQL injection, XSS, weak passwords, and misconfigurations across web applications.
- Automated crawling: Maps entire web applications.
- Login sequence recording: Scans password-protected areas.
- False-positive reduction technology: Improves reliability.
Acunetix is ideal for medium to large businesses with dynamic websites and custom applications. Its scanning engine prioritizes high-risk vulnerabilities, allowing companies to allocate resources effectively.

5. Burp Suite
Burp Suite is a powerful tool favored by security professionals and penetration testers. Unlike automated scanners designed for beginners, Burp Suite offers both automated scanning and extensive manual testing capabilities.
Main components include:
- Intercepting proxy for analyzing web traffic
- Automated vulnerability scanner
- Intruder tool for customized attack simulations
- Repeater tool for testing API security
Because of its depth and flexibility, Burp Suite is best suited for experienced developers and cybersecurity professionals. It allows users to replicate complex attack scenarios and verify vulnerabilities in detail.
6. Nikto
Nikto is an open-source web server scanner that performs comprehensive tests against web servers for dangerous files, outdated software versions, and configuration issues.
- Scans for over 6,700 known vulnerabilities
- Identifies outdated server components
- Detects default files and insecure configurations
As a command-line tool, Nikto requires technical expertise. However, it is highly effective for server administrators looking to assess infrastructure-level weaknesses. Since it is open-source, it is also cost-effective for startups and cybersecurity researchers.
7. WPScan
WPScan specializes in scanning WordPress websites for vulnerabilities within themes, plugins, and core files. Given WordPress’s widespread usage, it is a frequent target for attackers.
- Plugin vulnerability database
- Theme security checks
- User enumeration detection
WPScan’s regularly updated database makes it particularly valuable for WordPress site administrators. It highlights outdated extensions and provides actionable guidance to mitigate risk.

How to Choose the Right Website Security Scanner
Selecting the appropriate scanner depends on several factors:
- Website Complexity: Simple static websites may only require basic remote scanning tools, while dynamic web applications benefit from advanced automated scanners.
- Technical Expertise: Tools like Burp Suite and Nikto require professional-level experience, whereas Sucuri is beginner-friendly.
- Budget Considerations: Open-source tools minimize costs, while enterprise-level solutions provide deeper insights and automation.
- Compliance Requirements: Businesses subject to standards such as PCI DSS may require more comprehensive scanning and reporting features.
For optimal security posture, organizations often combine multiple tools. For example, pairing an SSL scanner with a full vulnerability scanner ensures both encryption integrity and application-level protection.
Best Practices for Ongoing Website Security
Using a scanner alone is not sufficient. Vulnerability detection must be part of a broader cybersecurity strategy. Best practices include:
- Regularly updating CMS, plugins, and themes
- Implementing strong password policies
- Enabling multi-factor authentication (MFA)
- Using a web application firewall (WAF)
- Backing up website data frequently
Continuous monitoring is critical. Cyber threats evolve rapidly, and a vulnerability that does not exist today may appear tomorrow due to newly discovered exploits. Automated weekly or daily scans significantly reduce exposure windows.
Why Regular Vulnerability Scanning Matters
Cyberattacks often exploit known vulnerabilities that have already been documented and patched. Unfortunately, many website owners delay updates or fail to conduct routine scans. Vulnerability scanners help identify:
- Unpatched software components
- Weak encryption protocols
- Configuration errors
- Common injection flaws
Early detection prevents data theft, service disruptions, financial losses, and reputational damage. For eCommerce sites and SaaS platforms, proactive scanning can mean the difference between secure operations and catastrophic data breaches.
Frequently Asked Questions (FAQ)
1. What is a website security scanner?
A website security scanner is a tool that automatically checks websites for vulnerabilities such as malware, outdated software, misconfigurations, and code injection flaws.
2. Are free website security scanners reliable?
Free scanners can detect common and surface-level vulnerabilities, but they may lack in-depth analysis and continuous monitoring features offered by paid solutions.
3. How often should a website be scanned for vulnerabilities?
Ideally, websites should be scanned at least weekly. High-traffic or eCommerce websites may require daily or continuous automated scanning.
4. Can a security scanner prevent cyberattacks?
Scanners do not prevent attacks directly. Instead, they detect vulnerabilities so they can be fixed before attackers exploit them.
5. Is SSL scanning necessary if HTTPS is enabled?
Yes. Simply enabling HTTPS does not guarantee secure configuration. SSL scanning ensures certificates, protocols, and ciphers meet modern security standards.
6. Do small websites really need vulnerability scanning?
Yes. Automated bots target websites of all sizes. Even small blogs can be compromised and used to distribute malware or spam.
7. Can multiple scanners be used together?
Absolutely. Combining scanners enhances detection coverage and provides a more comprehensive overview of website security posture.
By implementing the right combination of website security scanners and adopting consistent cybersecurity best practices, organizations can significantly reduce their vulnerability exposure and maintain user trust in an increasingly hostile digital environment.






