The internet most people use every day is only one visible layer of a much larger digital world. Search engines, social media platforms, online stores, news sites, and streaming services make up the surface web, but beneath that are private databases, restricted portals, and anonymous networks that are not indexed by Google or Bing. One of the most misunderstood parts of this hidden online environment is the dark web, a place often described with mystery, fear, and exaggeration.
TLDR: The dark web is a small part of the internet that requires special software, most commonly Tor Browser, to access. It is not automatically illegal, but it does host both legitimate privacy focused communities and criminal marketplaces. To access it safely, use trusted tools, avoid illegal content, protect your identity, never download suspicious files, and remember that anonymity is not the same as invincibility.
What Is the Dark Web?
The dark web refers to websites and services that exist on encrypted overlay networks and cannot be reached through ordinary browsers like Chrome, Safari, or Edge. The most common dark web network is Tor, short for The Onion Router. Tor websites usually end in .onion instead of familiar endings like .com or .org.
To understand the dark web clearly, it helps to separate the internet into three broad layers:
- Surface web: Public websites that search engines can index, such as blogs, online stores, and news sites.
- Deep web: Content hidden behind logins or forms, such as email inboxes, bank accounts, subscription libraries, medical portals, and company intranets.
- Dark web: A small section of the deep web that requires special software and is designed to provide anonymity for both visitors and site operators.
The dark web is often associated with illegal markets, stolen data, and hacking forums, but that is not the whole story. It is also used by journalists, whistleblowers, human rights activists, researchers, privacy advocates, and people living under censorship. In countries where open communication can be dangerous, the dark web may offer a way to read news, share information, or contact the outside world more safely.
Image not found in postmetaHow Does Tor Work?
Tor protects users by routing internet traffic through several volunteer operated servers, called nodes or relays. Instead of connecting directly to a website, your connection is wrapped in multiple layers of encryption and passed through different relays before reaching its destination. This is why it is called onion routing: each relay peels away one layer of encryption, but no single relay knows both who you are and where you are going.
This system makes it harder for websites, internet service providers, and outside observers to track browsing activity. However, it is important to understand that Tor is not magic. It does not protect you if you willingly reveal personal information, log into accounts tied to your real identity, download malware, or ignore basic security practices.
Is the Dark Web Illegal?
Accessing the dark web is not illegal in many countries. Tor itself is a privacy tool, and privacy tools have many legitimate uses. Visiting a legal news site through Tor, reading privacy guides, or communicating anonymously is generally lawful in most places.
However, the dark web can contain illegal material and services. Buying stolen data, drugs, weapons, counterfeit documents, malware, or anything that violates the law is still illegal, even if done through an anonymous network. The technology does not change the law. If an action is illegal on the regular internet, it is illegal on the dark web too.
Before using Tor, it is wise to understand your local laws and your personal risk level. In some regions, simply using privacy tools may attract attention, even when the activity itself is legal.
Why Do People Use the Dark Web?
People use the dark web for many reasons, ranging from responsible to risky. Some common legitimate uses include:
- Privacy protection: Users may want to browse without being tracked by advertisers or data brokers.
- Journalism: Reporters and sources may communicate through secure drop boxes.
- Whistleblowing: Individuals may share sensitive information while reducing the risk of retaliation.
- Anti censorship access: People in restricted environments may use Tor to reach blocked news or educational sites.
- Research: Cybersecurity analysts, academics, and investigators may study dark web trends to understand online threats.
At the same time, the dark web attracts scammers because anonymity makes trust difficult. Many dark web sites are unstable, short lived, or fraudulent. Even people seeking illegal goods are often cheated, hacked, or exposed. The dark web is not a secret paradise; it is a high risk environment where caution matters.
How to Access the Dark Web Safely
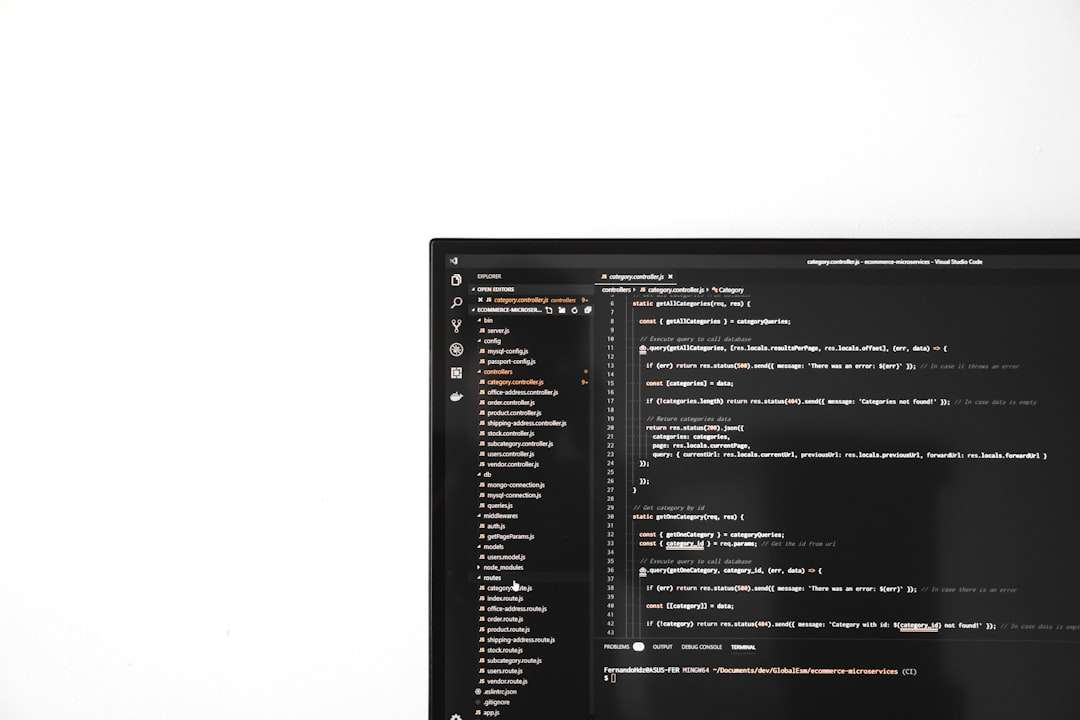
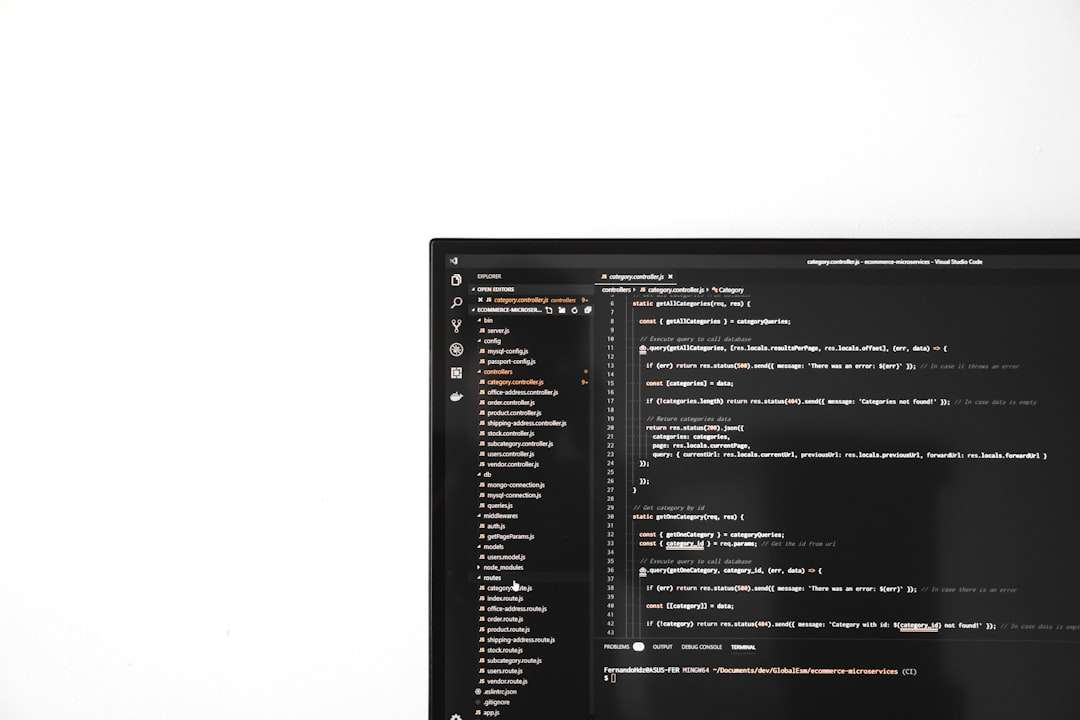
The safest way to access the dark web is to use the official Tor Browser, downloaded only from the official Tor Project website. Tor Browser is designed specifically for anonymous browsing and includes privacy protections that ordinary browsers do not provide.
- Download Tor Browser from the official source. Avoid third party download sites, ads, or random links, because modified installers may contain malware.
- Install updates promptly. Security patches matter. An outdated browser is easier to exploit.
- Use the default settings unless you understand the risks. Tor Browser is configured to reduce fingerprinting, and changing settings can make you more identifiable.
- Consider raising the security level. Tor Browser allows you to choose stronger security settings, which may disable risky web features such as some scripts.
- Visit only trusted onion addresses. Dark web links are easy to fake. Use reputable directories, official sources, or known organizations that publish their own onion addresses.
Should You Use a VPN with Tor?
Many beginners ask whether they should use a VPN with Tor. The answer depends on your goals and threat model. A VPN can hide Tor usage from your internet service provider, because your provider sees a connection to the VPN instead of directly to the Tor network. However, the VPN company can see that you are connecting to Tor, and you must trust it not to log or misuse that information.
For most casual privacy users, Tor Browser alone is often sufficient. If you choose to use a VPN, select a reputable provider with a strong privacy record, and avoid free VPNs that make money by collecting data. Do not assume that stacking tools automatically makes you anonymous. Poor habits can defeat even good technology.
Practical Safety Rules
When browsing the dark web, your behavior matters as much as your software. Follow these practical rules:
- Do not share personal information. Avoid using your real name, regular email address, phone number, workplace, school, or social media accounts.
- Do not log into personal accounts. Logging into accounts connected to your identity can link your Tor activity back to you.
- Do not download random files. Documents, images, archives, and software can contain malware or tracking elements.
- Do not enable unnecessary scripts or plugins. Extra browser features can increase tracking and security risks.
- Do not trust strangers or marketplaces. Scams are common, and anonymity makes accountability difficult.
- Never participate in illegal activity. The safest legal and ethical choice is to avoid criminal content entirely.
- Use strong device security. Keep your operating system updated, use antivirus protection where appropriate, and lock your device with a strong password.
Another important habit is compartmentalization. This means keeping your dark web activity separate from your everyday digital life. Do not reuse usernames, profile pictures, writing styles, passwords, or email addresses. Small details can create connections that reveal more than you expect.
Common Myths About the Dark Web
Myth one: The dark web is bigger than the regular internet. In reality, the dark web is much smaller than the surface web. The broader deep web is huge, but most of it is ordinary private content like databases and account pages.
Myth two: Tor makes you completely anonymous. Tor improves privacy, but it cannot protect against every mistake or every adversary. If you reveal your identity, download malware, or use unsafe habits, anonymity can collapse quickly.
Myth three: Everything on the dark web is illegal. Many onion services are legal and useful. Some major media organizations, privacy projects, and civil liberties groups have maintained onion sites to help users access information privately.
Myth four: You need advanced hacking skills to use it. Accessing Tor is technically simple. The real challenge is understanding the risks and behaving carefully.
What You Might Find There
Dark web content varies widely. You may find privacy forums, political discussion boards, encrypted communication services, cryptocurrency related communities, mirrors of news websites, and archives. You may also encounter disturbing, illegal, or fraudulent content. Because dark web sites are not regulated in the same way as mainstream platforms, quality and safety vary dramatically.

If you are simply curious, start with well known legal resources. Some reputable organizations publish official onion links on their normal websites. This is much safer than clicking through random link lists, many of which are outdated, misleading, or intentionally malicious.
Warning Signs to Avoid
Leave immediately if a site asks you to install special software, open an unknown file, disable security settings, provide personal information, or make suspicious payments. Be especially cautious of sites promising illegal goods, hacking services, leaked accounts, or guaranteed anonymity. These are often scams, law enforcement traps, malware delivery pages, or all three.
Also be careful with screenshots and copying text. Documents can accidentally include metadata, and screenshots may reveal device details, tabs, usernames, or time zones. If privacy matters, slow down and check what you are exposing before you share anything.
Final Thoughts
The dark web is neither a mythic criminal underworld nor a harmless playground. It is a privacy focused part of the internet that can be used for both important legitimate purposes and serious crimes. The same anonymity that protects activists and journalists can also protect scammers and criminals, which is why careful judgment is essential.
If you decide to explore it, use Tor Browser, keep your software updated, avoid illegal content, protect your identity, and treat every unknown site with skepticism. The best safety strategy is simple: be curious, but not careless. On the dark web, privacy is possible, but it is earned through discipline, awareness, and responsible choices.